Research shows that deploying AI agents in a security operations center can shrink average cyber‑incident response time by roughly one third. A typical outage lasts eight to twelve hours; cutting three quarters of that saves up to four hours per incident. For large enterprises, the faster remediation translates into multi‑million‑dollar annual cost reductions.
An AI agent gathers telemetry, enriches each event, and proposes possible actions, but the final decision stays with the analyst. If the agent is granted authority to isolate nodes or launch countermeasures on its own, the risk of false blocks rises sharply. Pattern‑matching errors can trigger unnecessary shutdowns or even inject malicious cues, potentially crippling critical services.
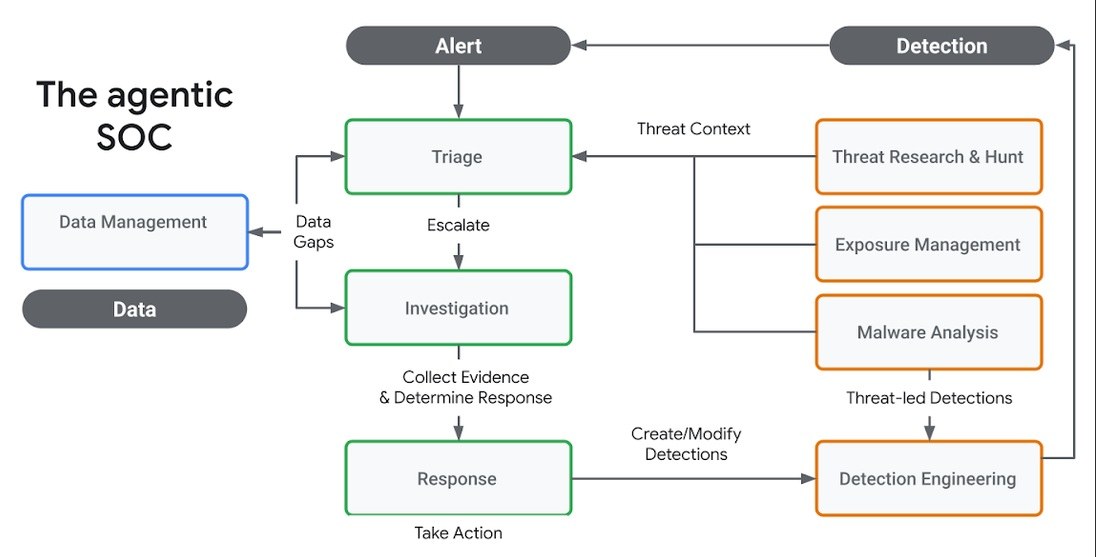
The optimal approach is a hybrid model. Automation handles alert triage, context enrichment, and report preparation. A human remains in the loop for selecting isolation scenarios, assessing risk, and authorizing response actions. This preserves AI speed while keeping outcomes under reliable supervision.
For you, this means faster incident handling, reduced downtime, and lower financial loss. The mandatory human‑in‑the‑loop safeguards against false isolations and protects your company’s reputation.
Why this matters: Accelerated response cuts outage costs and improves service continuity. Keeping an analyst in the decision loop prevents costly mistakes and shields brand trust.